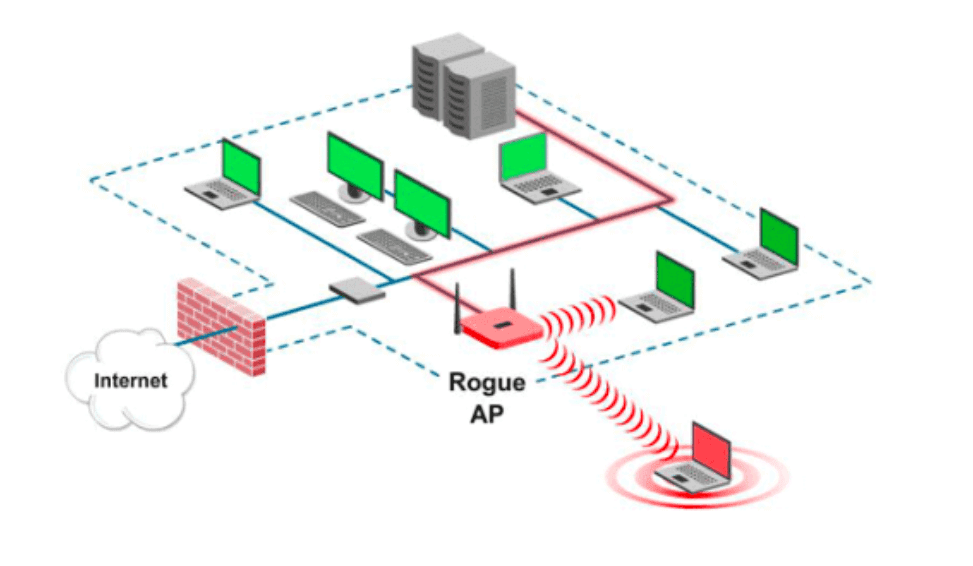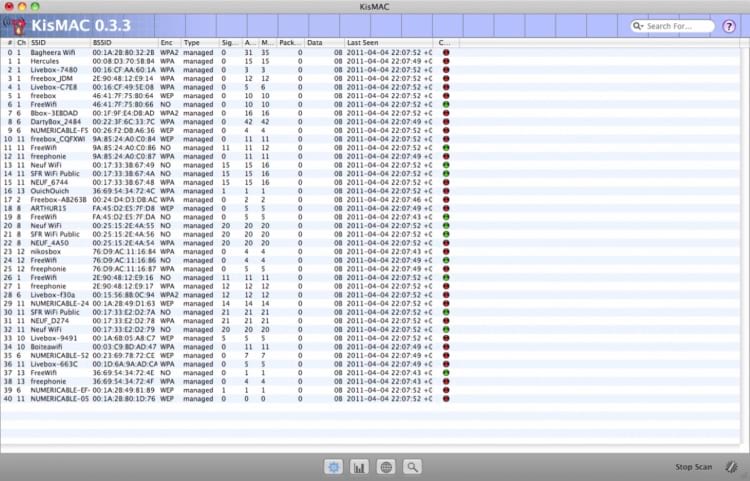
mitmAP - An Open Source Tool to Create a Fake Access Point and Sniff Data - Latest Hacking News | Cyber Security News, Hacking Tools and Penetration Testing Courses
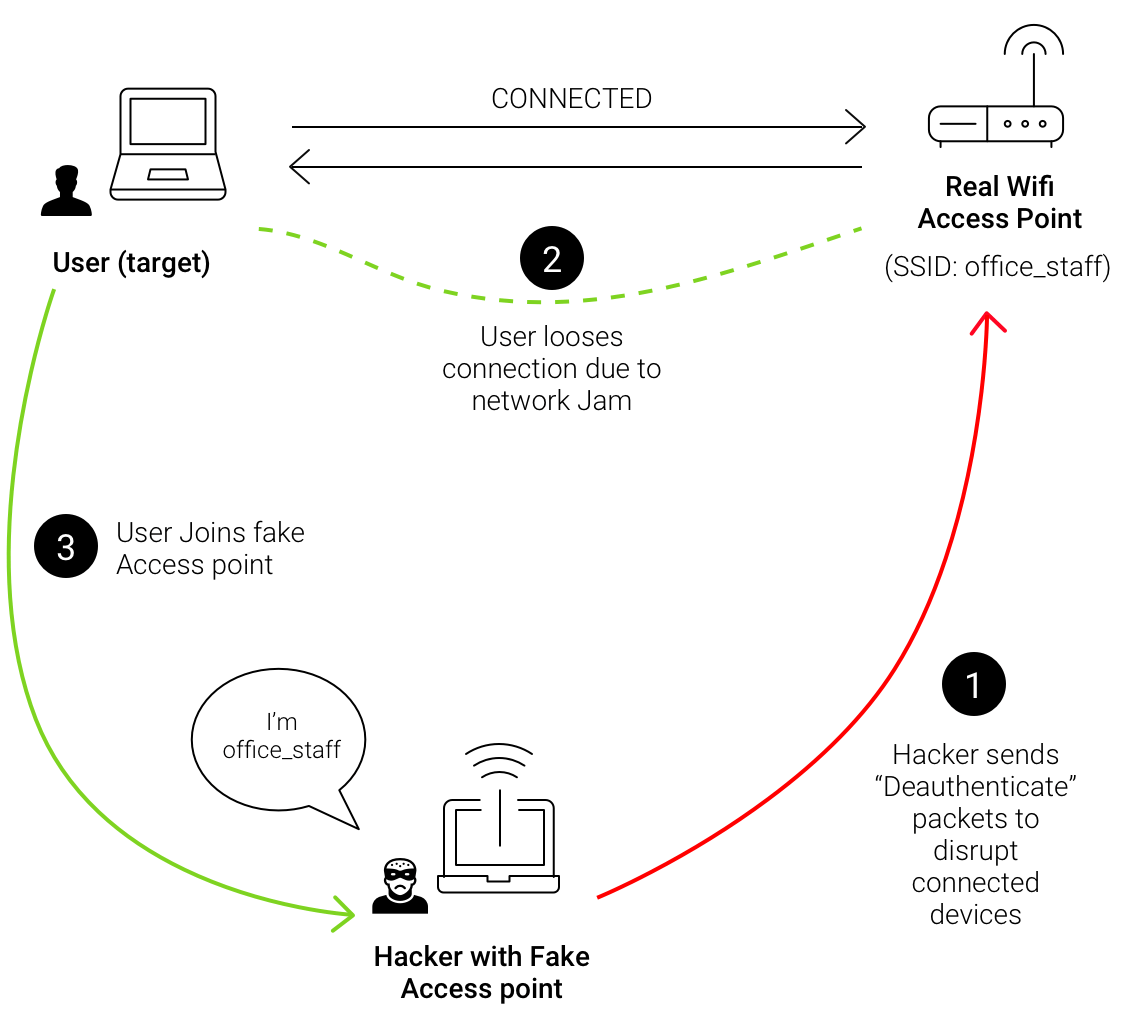
![PenTest Edition: Creating an Evil Twin or Fake Access Point on Your Home Network Using Aircrack-ng and Dnsmasq [Part 1 – Setup] – The Cybersecurity Man PenTest Edition: Creating an Evil Twin or Fake Access Point on Your Home Network Using Aircrack-ng and Dnsmasq [Part 1 – Setup] – The Cybersecurity Man](https://thecybersecuritymancom.files.wordpress.com/2018/08/fake-ap-image.png?w=925)
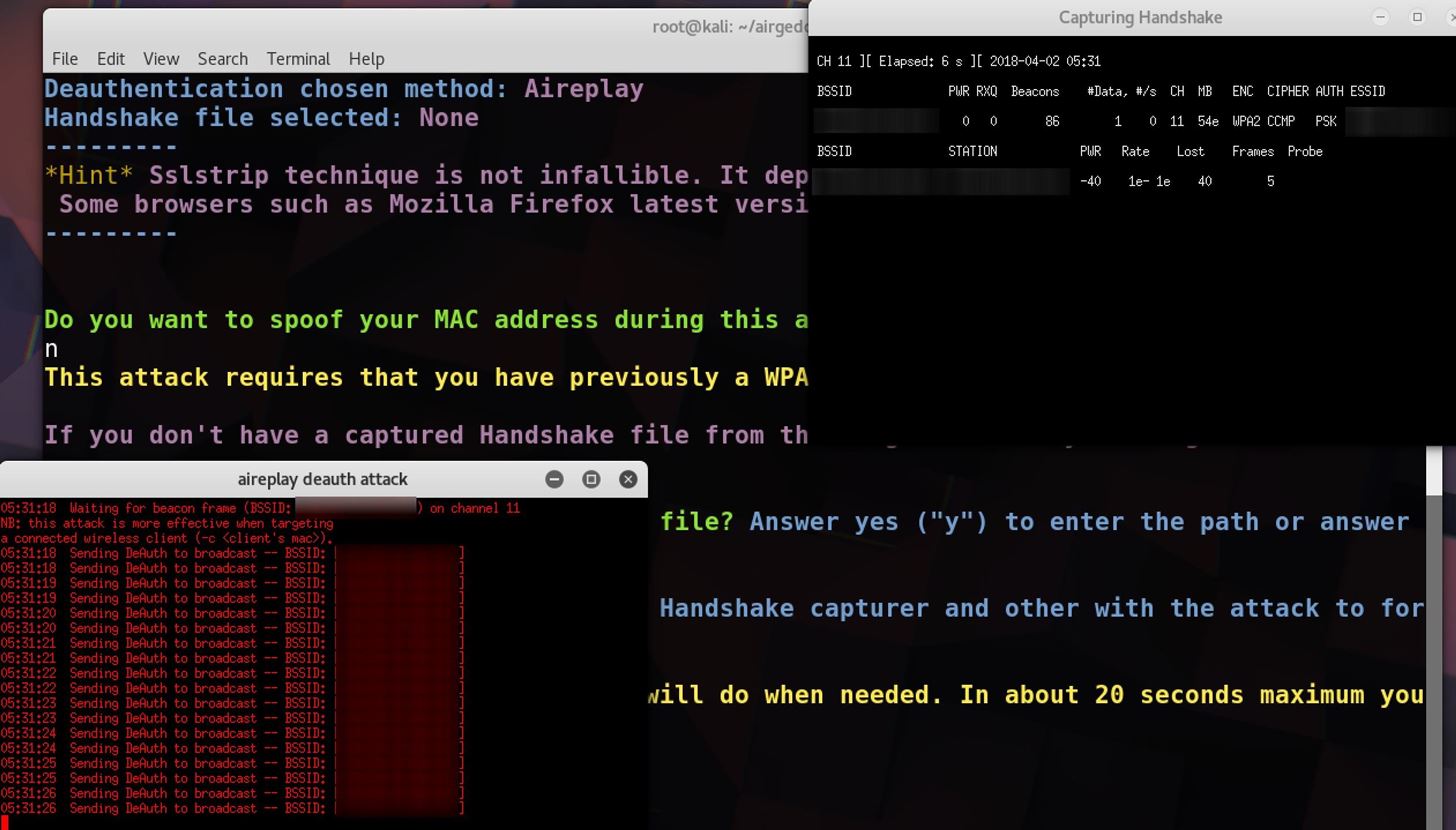
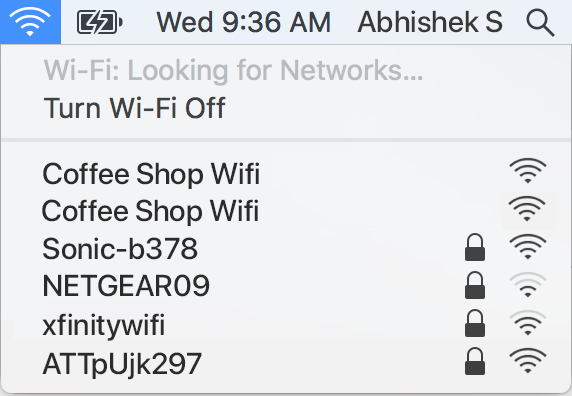
PenTest Edition: Creating an Evil Twin or Fake Access Point on Your Home Network Using Aircrack-ng and Dnsmasq [Part 1 – Setup] – The Cybersecurity Man
How to Hack Wi-Fi: Creating an Evil Twin Wireless Access Point to Eavesdrop on Data « Null Byte :: WonderHowTo